new Ransomware strain It makes rounds online that can encrypt your files faster than most, as it uses a popular third-party Windows search tool to figure out exactly what you’re looking for.
It was first discovered in June last year Trend MicroThis new strain of ransomware is named Mimic based on a string that the company’s security researchers found in its binaries. according to New report (Opens in a new tab)So far, Mimic ransomware is mainly used to target Russian and English speaking users.
Interestingly, PC (Opens in a new tab) indicates that some of the code in Mimic shares similarities with Conti. This is likely due to the fact that Conti’s source code was leaked back in March 2022 by a Ukrainian researcher after its creators sided with Russia.
Mimic ransomware is currently spread through executable files (.exe) that are sent to targeted victims via email. Once opened, the executable extracts its malicious payload along with the tools used for disabling Windows Defender on the victim’s computer.
Mimic has a few tricks to help speed up the process of encrypting victim files, including using multiple processor threats and command-line arguments to narrow file targeting.
What makes Mimic so much faster and more efficient than previous ransomware strains is how it uses its “everything” search tool to locate hostage files. Everything is developed by Voidtools, a file name search engine for Windows that is much more efficient and faster than Windows Search.
With everything on a target system, Mimic is able to locate files that can be encrypted, such as documents, while avoiding system files that would prevent the computer from booting in the first place if locked.
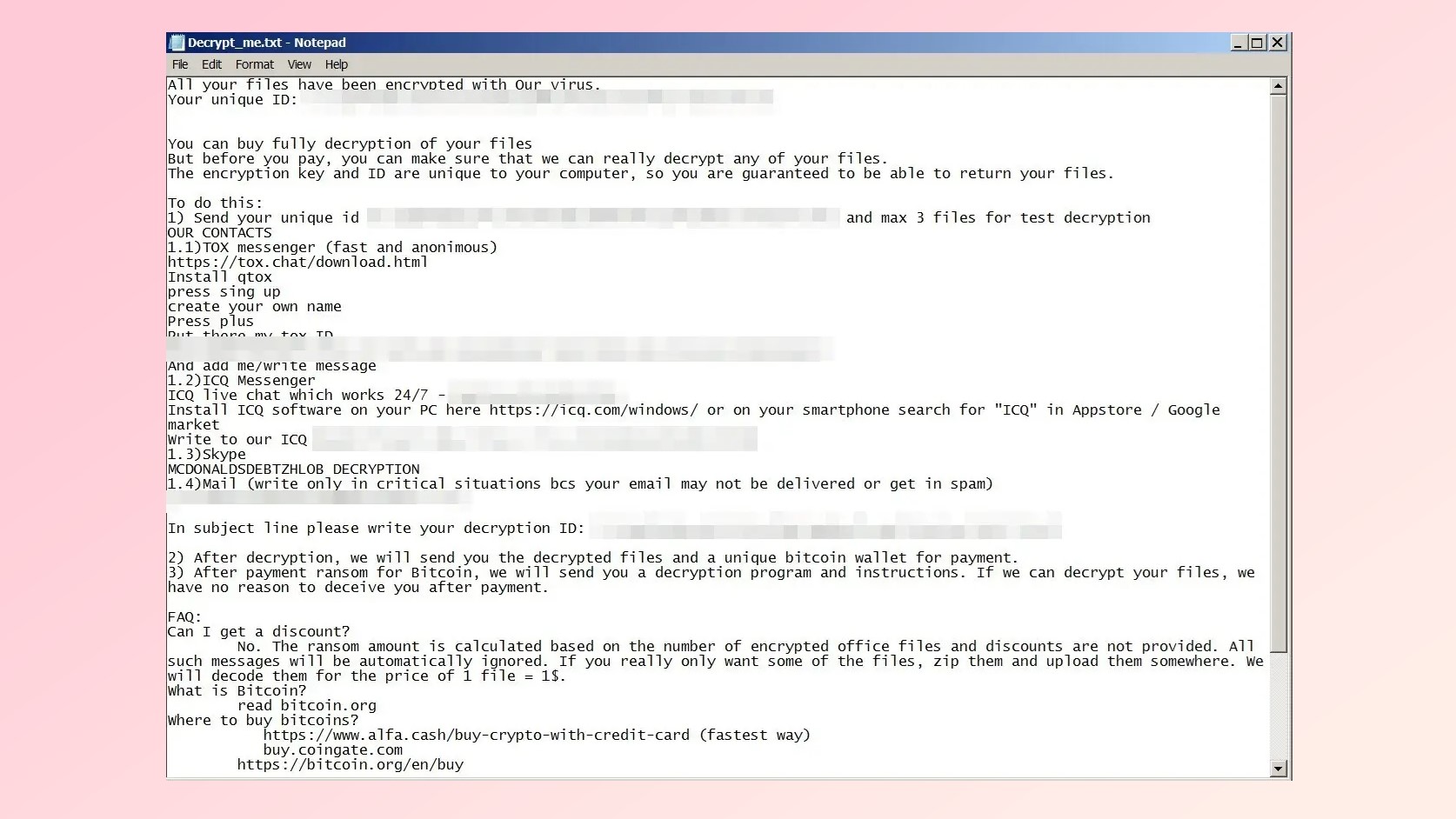
Files encrypted by Mimic ransomware are given the extension “.QUIETPLACE” and a ransom note named “Decrypt_me.txt” is dropped somewhere on the user’s system. This ransom note explains that victims need to pay the attackers in bitcoin for their files to be unencrypted. However, it also says that attackers can decrypt only some of the victim’s most important files for the price of “1 file = $1”. This might be worth it to victims if they only need a few files from their locked system and were planning on upgrading to a new computer anyway.
This is the first time we’ve seen a string of ransomware use a popular third-party tool to speed up the encryption process. The Find Everything tool does not need to be installed on the victim’s machine, as it is built into the malicious executable used to infect the computer with Mimic in the first place.
How to stay safe from ransomware

Just as with other malware and viruses, you should avoid opening attachments in emails from unknown senders to stay safe from ransomware. Likewise, you should not download illegal software or download any file from sites without an established reputation.
the The best antivirus software It can also detect many types of ransomware before it infects your system. However, the antivirus is not able to open your files once they have been locked by an attacker with ransomware. For this reason, it is useful to use a The best cloud storage To keep an extra copy of your most important files securely stored in the cloud and The best cloud backup services It might be a better option as it backs up your files automatically.
If you have fallen victim to ransomware, this is it Step by step guide It can guide you through the process of restoring your files. At the same time, Bitdefender And other cyber security companies often Ransomware decryption tools (Opens in a new tab) Like I did with Darkside ransomware. This way, even if you don’t have the money or don’t want to pay a ransom to cyber criminals, there’s still a chance you’ll get your files back one day.
As for Mimic ransomware, it is a relatively new strain and we don’t know much about how it is used in attacks or who is behind it yet. We hope to find out more soon.
[ad_2]




